- Главная
- Проекты
Проекты
Путешествия Фёдора Конюхова
1977-1985
1986-1994
1995-2003
2004-2012
2013-2018
2019-2024
07 августа 2020 совершил восхождение на гору Эльбрус (Западная вершина) с сыновьями Оскаром и Николаем, и внучкой Полиной.
2020 год03 января 2020г совершил восхождение на гору Килиманджаро (Африка) 5895м с сыновьями Оскаром и Николаем, и внуком Аркадием.
2020 годС 6 декабря 2018 по 9 мая 2019 совершил первый в истории океанской гребли успешный переход через Южный океан от Новой Зеландии (город Данедин) до пролива Дрейка (острова Диего-Рамирез, Чили) на вёсельной лодке «АКРОС». Пройдено по лагу 11 525 километров (6 402 морские мили) за 154 дня 13 часов и 37 минут.
2018 годПервый, в истории России, одиночный поход к Южному полюсу с последующим восхождением на высшую точку Антарктиды — массив Винсон (4892 м). Стартовал с залива Геркулес (Hercules Bay) 8 ноября 1995г. — достиг Южного полюса 5 января 1996г.
1995 годУчастие в международной регате «Кубок Балтики-80» в составе экипажа ДВВИМУ (Владивосток)
1980 годВосхождение на высочайшую гору Алтая — Белуха (4 506 метров) с младшим сыном Николаем Конюховым (13 лет)
2018 годСовместно с Иваном Меняйло установление мирового рекорда продолжительности полета на тепловом аэростате «Бинбанк Премиум». Объем оболочки 10 000 кубических метров (АХ — 12). Продолжительность полета 55 часов и 9 минут
2017 годСовместно с Иваном Меняйло установление мирового рекорда продолжительности полета на тепловом аэростате «Бинбанк». Объем оболочки 4 000 кубических метров (АХ-9). Продолжительность полета 32 часа 12 минут
2016 годПопытка пересечь ледник Гренландии на буере (тримаран на лыжах и под парусом). Проект не осуществил
2006 годВосхождение на массив Винсон (Антарктида) в рамках программы «Семь вершин мира». 19 января 1996г.
1996 год

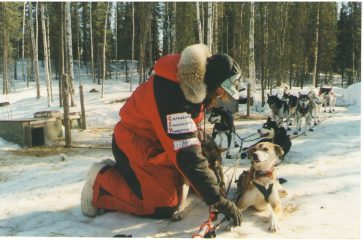
Гонка на собачьих упряжках Iditarod через Аляску по маршруту Анкоридж – Ном. Протяженность маршрута 1 600 километров. Получил приз Национального Банка Аляски — «Red Lantern»
2000 годУчастие в европейских регатах Sardinia Cup (Италия), Gotland Race (Швеция), Cowes week (Англия) в составе экипажа макси-яхты «Grand Mistral» (80 футов)
1997 годВосхождение на пик Мак-Кинли (Северная Америка), совместно с Владимиром Яночкиным (Москва) в рамках программы «Семь вершин мира». 26 мая 1997г.
1997 годУчастник первой российской автономной экспедиции «Арктика» под руководством Владимира Чукова к Северному полюсу. Старт 04 марта 1989г. с архипелага Северная Земля, остров Шмита. Экспедиция достигла Северного полюса 6 мая 1989г.
1989 годОдиночный кругосветный полет на воздушном шаре «МОРТОН». Старт 12 июля 2016 в Австралии (аэродром Нортхэм). Установил два мировых рекорда FAI: 268 часов и 33 521 километр. Удостоен звания FAI Пилот года 2016. Награжден дипломом FAI Montgolfier и медалью de La Vaulx
2016 годСовместная экспедиция с Виктором Симоновым на собачьих упряжках «Онежское Поморье 2016»
2016 годУстановление мирового рекорда продолжительности полета на тепловом аэростате «Бинбанк», объемом 3950 м3.
2016 год
Установление российского рекорда по продолжительности полета на тепловом аэростате «Бинбанк» класса АХ-9 объемом 3950 кубических метров — 19 часов 10 минут.
2015 год


2013-2014 (декабрь-май) Тихоокеанский переход на весельной лодке от континента до континента, без заходов в порты, без посторонней помощи за рекордное время — 160 дней по маршруту Чили (Кон Кон) – Австралия (Мулулуба), преодолел 9 400 морских миль (17 408 километров).
2013 годСовместно с Виктором Симоновым пересек Северный Ледовитый океан на собачьей упряжке по маршруту: Северный полюс – Канада (остров Уорт Хант). 46 суток в пути
2013 год


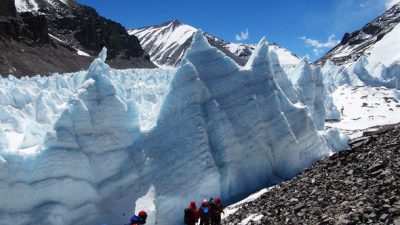





Восхождение на вершину Эвереста по Северному хребту (со стороны Тибета) в составе российской команды «7 Вершин»
2012 годЭкспедиция «9 высочайших вершин Эфиопии»
2011 годII этап международной экспедиции «По следам Великого Шелкового Пути 2009» через Монголию
2009 годОдиночное плавание вокруг Антарктиды «Antarctica Cup» по маршруту Олбани (Западная Австралия) – мыс Горн – мыс Доброй Надежды – мыс Луин — Олбани (Западная Австралия). 102 дня
2007 годПересечение Гренландии на собачьих упряжках от восточного побережья (поселок Исорток) через ледовый купол до западного побережья (поселок Иллулисат), вдоль Полярного круга. 16 дней
2007 годОрганизация испытаний экспериментального полярного буера на восточном побережье Гренландии
2006 годПереход с российским экипажем на яхте «Алые Паруса», по маршруту Англия – Канарские о-ва – о. Барбадос – о. Антигуа – Англия
2005 годОдиночное кругосветное плавание на макси-яхте «ТС «Алые Паруса» по маршруту Фалмут (Англия) – Хобарт (о. Тасмания) – Фалмут (Англия)
2004 годОдиночный трансатлантический переход с востока на запад на макси-яхте «ТС «Алые Паруса» по маршруту Канарские острова (о. Ла Гомера) — Барбадос (Порт Сент Чарльз)
2004 годСовместный Российско-Британский трансатлантический переход с экипажем на макси-катамаране «ТС «Алые Паруса» по маршруту Ямайка (Montega Bay) — Англия (Lands End). Шкипер Tony Bullimore
2003 годСовместный Российско-Британский трансатлантический переход с экипажем на макси-катамаране «ТС «Алые Паруса» по маршруту Канарские острова (о. Ла Гомера) – о. Барбадос. . Шкипер Tony Bullimore
2003 год
Пересечение Атлантического океана на гребной лодке «УРАЛАЗ». Маршрут: Канарские острова (о. Ла Гомера) – о. Барбадос. Новый мировой рекорд — 46 суток. Старт 16 октября 2002г. — финиш 01 декабря 2002г. Лодка «Уралаз» находится в музее, на территории комплекса Золотой пляж, на озере Тургояк
2002 год




Экспедиции на верблюдах «По следам Великого Шелкового Пути-2002». Маршрут: Калмыкия, Астрахань, Дагестан, Ставропольский край, Волгоградская область, Калмыкия. Пройдено 1050 км. Караван состоял из 13 верблюдов. Старт 04 апреля 2002г. — финиш в Элисте 12 июня 2002г.
2002 годОдиночная кругосветная гонка нон-стоп «Vendee Globe». Старт во Франции. По техническим причинам вынужден был совершить заход в Сидней (Автсралия) и выбыл из гонки
2000 годОдиночная кругосветная гонка «Around Alone» по маршруту: США — Кейптаун (ЮАР) — Новая Зеландия — Уругвай — США. Третье одиночное кругосветное плавание
1998 годВосхождение на пик Косцюшко (Австралия) в рамках программы «Семь вершин мира». 17 апреля 1997г.
1997 год
Восхождение на Килиманджаро (Африка) в рамках программы «Семь вершин мира». 18 февраля 1997г.
1997 годВосхождение на Аконкагуа (Южная Америка) в рамках программы «Семь вершин мира». 09 марта 1996г.
1996 годКругосветная экспедиция на двухмачтовом кече «Формоза» (56 футов) по маршруту: Тайвань – Гонконг – Сингапур – остров Вэ (Индонезия) – остров Виктория (Сейшельские острова) – Йемен (порт Аден) – Джидда (Саудовская Аравия) – Суэцкий канал – Александрия (Египет) – Гибралтар – Касабланка (Марокко) – Санта Люсия (Карибские острова) – Панамский канал – Гонолулу (Гавайские острова) – Марианские острова – Тайвань. Старт 25 марта 1993г. остров Тайвань, бухта Килунь — финиш 26 августа 1994г. остров Тайвань. Затем яхта Формоза была доставлена в Находку, Россия. В настоящий момент принадлежит Федерации Парусного Спорта Приморского края и называется «ВЕСТА».
1993 годВосхождение на Эверест (Азия) совместно с Евгением Виноградским (Екатеринбург) в рамках программы «Семь вершин мира». 14 мая 1992г.
1992 годВосхождение на Эльбрус (Европа) в рамках программы «Семь вершин мира». 26 февраля 1992г.
1992 годОрганизатор российско-австралийского автопробега на внедорожниках по маршруту Находка — Москва; Съемки документального фильма «Через Красную Неизвестность» телеканалом SBS (Австралия). Старт 05 августа 1991г. — финиш 15 сентября 1991г.
1991 годПервое, в истории России, одиночное кругосветное плавание нон-стоп на яхте «Караана» (36 футов/Swanson) по маршруту Сидней – Мыс Горн – Экватор — Сидней (Австралия) за 224 дня. Старт 28 октября 1990г. — финиш 08 июня 1991г.
1991 годПервый, в истории России, одиночный поход на лыжах к Северному полюсу. Стартовал с мыса Локоть, остров Средний 3 марта. Достиг полюса 8 мая 1990г. Время в пути — 72 дня
1990 годСовместный Советско-Американский трансконтинентальный велопробег Находка — Москва – Ленинград. Руководитель пробега с российской стороны. Старт 18 июня 1989г. – финиш 26 октября 1989г.
1989 годУчастник трансарктической лыжной экспедиции СССР — Северный полюс – Канада в составе международной группы при поддержке газеты «Комсомольская Правда». Старт: Северная Земля, остров Средний, мыс Арктический 03 марта 1988г. Группа достигала Северного полюса 24 апреля 1988г. и финишировала в Канаде, остров Уорт Хант 01 июня 1988г.
1988 годЛыжная экспедиция по Баффиновой Земле (Канада) в составе советско-канадской экспедиции (подготовка к походу на Северный Полюс)
1987 годЛыжный переход в полярную ночь к Полюсу относительной недоступности в Северном Ледовитом океане в составе экспедиции газеты «Комсомольская Правда». Группа достигла полюса — 27 января 1986г.
1986 годЭкспедиция через Уссурийскую тайгу по следам В.К. Арсеньева и Дерсу Узала
1985 годСплав на плоту по реке Лена. Участие в международной регате на Кубок Балтики-84 в составе экипажа ДВВИМУ (Владивосток)
1984 годЛыжная научно-спортивная экспедиция в море Лаптевых. Первая полярная экспедиция в составе группы Дмитрия Шпаро
1983 годПересечение Чукотки на собачьей упряжке
1981 годII этап экспедиции на яхте «Чукотка» по маршруту Владивосток — Сахалин — Камчатка — Командорские острова; восхождение на вулкан Ключевский
1979 годЭкспедиция на яхте «Чукотка» по маршруту Витуса Беринга
1978 годЭкспедиция на яхте «Чукотка» по маршруту Витуса Беринга
1977 год- 1977
- Экспедиция на яхте «Чукотка» по маршруту Витуса Беринга
- 1978
- Экспедиция на яхте «Чукотка» по маршруту Витуса Беринга
- 1979
- II этап экспедиции на яхте «Чукотка» по маршруту Владивосток — Сахалин — Камчатка — Командорские острова; восхождение на вулкан Ключевский
- 1980
- Участие в международной регате «Кубок Балтики-80» в составе экипажа ДВВИМУ (Владивосток)
- 1981
- Пересечение Чукотки на собачьей упряжке
- 1983
- Лыжная научно-спортивная экспедиция в море Лаптевых. Первая полярная экспедиция в составе группы Дмитрия Шпаро
- 1984
- Сплав на плоту по реке Лена. Участие в международной регате на Кубок Балтики-84 в составе экипажа ДВВИМУ (Владивосток)
- 1985
- Экспедиция через Уссурийскую тайгу по следам В.К. Арсеньева и Дерсу Узала
- 1986
- Лыжный переход в полярную ночь к Полюсу относительной недоступности в Северном Ледовитом океане в составе экспедиции газеты «Комсомольская Правда». Группа достигла полюса — 27 января 1986г.
- 1987
- Лыжная экспедиция по Баффиновой Земле (Канада) в составе советско-канадской экспедиции (подготовка к походу на Северный Полюс)
- 1988
- Участник трансарктической лыжной экспедиции СССР — Северный полюс – Канада в составе международной группы при поддержке газеты «Комсомольская Правда». Старт: Северная Земля, остров Средний, мыс Арктический 03 марта 1988г. Группа достигала Северного полюса 24 апреля 1988г. и финишировала в Канаде, остров Уорт Хант 01 июня 1988г.
- 1989
- Совместный Советско-Американский трансконтинентальный велопробег Находка — Москва – Ленинград. Руководитель пробега с российской стороны. Старт 18 июня 1989г. – финиш 26 октября 1989г.
- 1989
- Участник первой российской автономной экспедиции «Арктика» под руководством Владимира Чукова к Северному полюсу. Старт 04 марта 1989г. с архипелага Северная Земля, остров Шмита. Экспедиция достигла Северного полюса 6 мая 1989г.
- 1990
- Первый, в истории России, одиночный поход на лыжах к Северному полюсу. Стартовал с мыса Локоть, остров Средний 3 марта. Достиг полюса 8 мая 1990г. Время в пути — 72 дня
- 1991
- Первое, в истории России, одиночное кругосветное плавание нон-стоп на яхте «Караана» (36 футов/Swanson) по маршруту Сидней – Мыс Горн – Экватор — Сидней (Австралия) за 224 дня. Старт 28 октября 1990г. — финиш 08 июня 1991г.
- 1991
- Организатор российско-австралийского автопробега на внедорожниках по маршруту Находка — Москва; Съемки документального фильма «Через Красную Неизвестность» телеканалом SBS (Австралия). Старт 05 августа 1991г. — финиш 15 сентября 1991г.
- 1992
- Восхождение на Эльбрус (Европа) в рамках программы «Семь вершин мира». 26 февраля 1992г.
- 1992
- Восхождение на Эверест (Азия) совместно с Евгением Виноградским (Екатеринбург) в рамках программы «Семь вершин мира». 14 мая 1992г.
- 1993
- Кругосветная экспедиция на двухмачтовом кече «Формоза» (56 футов) по маршруту: Тайвань – Гонконг – Сингапур – остров Вэ (Индонезия) – остров Виктория (Сейшельские острова) – Йемен (порт Аден) – Джидда (Саудовская Аравия) – Суэцкий канал – Александрия (Египет) – Гибралтар – Касабланка (Марокко) – Санта Люсия (Карибские острова) – Панамский канал – Гонолулу (Гавайские острова) – Марианские острова – Тайвань. Старт 25 марта 1993г. остров Тайвань, бухта Килунь — финиш 26 августа 1994г. остров Тайвань. Затем яхта Формоза была доставлена в Находку, Россия. В настоящий момент принадлежит Федерации Парусного Спорта Приморского края и называется «ВЕСТА».
- 1995
- Первый, в истории России, одиночный поход к Южному полюсу с последующим восхождением на высшую точку Антарктиды — массив Винсон (4892 м). Стартовал с залива Геркулес (Hercules Bay) 8 ноября 1995г. — достиг Южного полюса 5 января 1996г.
- 1996
- Восхождение на Аконкагуа (Южная Америка) в рамках программы «Семь вершин мира». 09 марта 1996г.
- 1996
- Восхождение на массив Винсон (Антарктида) в рамках программы «Семь вершин мира». 19 января 1996г.
- 1997
- Восхождение на Килиманджаро (Африка) в рамках программы «Семь вершин мира». 18 февраля 1997г.
- 1997
- Восхождение на пик Косцюшко (Австралия) в рамках программы «Семь вершин мира». 17 апреля 1997г.
- 1997
- Восхождение на пик Мак-Кинли (Северная Америка), совместно с Владимиром Яночкиным (Москва) в рамках программы «Семь вершин мира». 26 мая 1997г.
- 1997
- Участие в европейских регатах Sardinia Cup (Италия), Gotland Race (Швеция), Cowes week (Англия) в составе экипажа макси-яхты «Grand Mistral» (80 футов)
- 1998
- Одиночная кругосветная гонка «Around Alone» по маршруту: США — Кейптаун (ЮАР) — Новая Зеландия — Уругвай — США. Третье одиночное кругосветное плавание
- 2000
- Одиночная кругосветная гонка нон-стоп «Vendee Globe». Старт во Франции. По техническим причинам вынужден был совершить заход в Сидней (Автсралия) и выбыл из гонки
- 2000
- Гонка на собачьих упряжках Iditarod через Аляску по маршруту Анкоридж – Ном. Протяженность маршрута 1 600 километров. Получил приз Национального Банка Аляски — «Red Lantern»
- 2002
- Экспедиции на верблюдах «По следам Великого Шелкового Пути-2002». Маршрут: Калмыкия, Астрахань, Дагестан, Ставропольский край, Волгоградская область, Калмыкия. Пройдено 1050 км. Караван состоял из 13 верблюдов. Старт 04 апреля 2002г. — финиш в Элисте 12 июня 2002г.
- 2002
- Пересечение Атлантического океана на гребной лодке «УРАЛАЗ». Маршрут: Канарские острова (о. Ла Гомера) – о. Барбадос. Новый мировой рекорд — 46 суток. Старт 16 октября 2002г. — финиш 01 декабря 2002г. Лодка «Уралаз» находится в музее, на территории комплекса Золотой пляж, на озере Тургояк
- 2003
- Совместный Российско-Британский трансатлантический переход с экипажем на макси-катамаране «ТС «Алые Паруса» по маршруту Канарские острова (о. Ла Гомера) – о. Барбадос. . Шкипер Tony Bullimore
- 2003
- Совместный Российско-Британский трансатлантический переход с экипажем на макси-катамаране «ТС «Алые Паруса» по маршруту Ямайка (Montega Bay) — Англия (Lands End). Шкипер Tony Bullimore
- 2004
- Одиночный трансатлантический переход с востока на запад на макси-яхте «ТС «Алые Паруса» по маршруту Канарские острова (о. Ла Гомера) — Барбадос (Порт Сент Чарльз)
- 2004
- Одиночное кругосветное плавание на макси-яхте «ТС «Алые Паруса» по маршруту Фалмут (Англия) – Хобарт (о. Тасмания) – Фалмут (Англия)
- 2005
- Переход с российским экипажем на яхте «Алые Паруса», по маршруту Англия – Канарские о-ва – о. Барбадос – о. Антигуа – Англия
- 2006
- Попытка пересечь ледник Гренландии на буере (тримаран на лыжах и под парусом). Проект не осуществил
- 2006
- Организация испытаний экспериментального полярного буера на восточном побережье Гренландии
- 2007
- Пересечение Гренландии на собачьих упряжках от восточного побережья (поселок Исорток) через ледовый купол до западного побережья (поселок Иллулисат), вдоль Полярного круга. 16 дней
- 2007
- Одиночное плавание вокруг Антарктиды «Antarctica Cup» по маршруту Олбани (Западная Австралия) – мыс Горн – мыс Доброй Надежды – мыс Луин — Олбани (Западная Австралия). 102 дня
- 2009
- II этап международной экспедиции «По следам Великого Шелкового Пути 2009» через Монголию
- 2011
- Экспедиция «9 высочайших вершин Эфиопии»
- 2012
- Восхождение на вершину Эвереста по Северному хребту (со стороны Тибета) в составе российской команды «7 Вершин»
- 2013
- 2013-2014 (декабрь-май) Тихоокеанский переход на весельной лодке от континента до континента, без заходов в порты, без посторонней помощи за рекордное время — 160 дней по маршруту Чили (Кон Кон) – Австралия (Мулулуба), преодолел 9 400 морских миль (17 408 километров).
- 2013
- Совместно с Виктором Симоновым пересек Северный Ледовитый океан на собачьей упряжке по маршруту: Северный полюс – Канада (остров Уорт Хант). 46 суток в пути
- 2014
- Фёдор Конюхов на вёслах через Тихий океан — Проект завершен
- 2015
- Установление российского рекорда по продолжительности полета на тепловом аэростате «Бинбанк» класса АХ-9 объемом 3950 кубических метров — 19 часов 10 минут.
- 2016
- Установление мирового рекорда продолжительности полета на тепловом аэростате «Бинбанк», объемом 3950 м3.
- 2016
- Одиночный кругосветный полет на воздушном шаре «МОРТОН». Старт 12 июля 2016 в Австралии (аэродром Нортхэм). Установил два мировых рекорда FAI: 268 часов и 33 521 километр. Удостоен звания FAI Пилот года 2016. Награжден дипломом FAI Montgolfier и медалью de La Vaulx
- 2016
- Совместная экспедиция с Виктором Симоновым на собачьих упряжках «Онежское Поморье 2016»
- 2016
- Совместно с Иваном Меняйло установление мирового рекорда продолжительности полета на тепловом аэростате «Бинбанк». Объем оболочки 4 000 кубических метров (АХ-9). Продолжительность полета 32 часа 12 минут
- 2017
- Совместно с Иваном Меняйло установление мирового рекорда продолжительности полета на тепловом аэростате «Бинбанк Премиум». Объем оболочки 10 000 кубических метров (АХ — 12). Продолжительность полета 55 часов и 9 минут
- 2018
- Восхождение на высочайшую гору Алтая — Белуха (4 506 метров) с младшим сыном Николаем Конюховым (13 лет)
- 2018
- 1 ЭТАП — Кругосветный переход на весельной лодке «АКРОС» в Южном полушарии
- 2018
- С 6 декабря 2018 по 9 мая 2019 совершил первый в истории океанской гребли успешный переход через Южный океан от Новой Зеландии (город Данедин) до пролива Дрейка (острова Диего-Рамирез, Чили) на вёсельной лодке «АКРОС». Пройдено по лагу 11 525 километров (6 402 морские мили) за 154 дня 13 часов и 37 минут.
- 2020
- 07 августа 2020 совершил восхождение на гору Эльбрус (Западная вершина) с сыновьями Оскаром и Николаем, и внучкой Полиной.
- 2020
- 03 января 2020г совершил восхождение на гору Килиманджаро (Африка) 5895м с сыновьями Оскаром и Николаем, и внуком Аркадием.
- 2020
- Восхождение на гору Эльбрус 2020
- 2020
- Восхождение на Килиманджаро 2020
- 2021
- Полет в стратосферу на высоту 25 километров. Установление абсолютного рекорда высоты для теплового аэростата
- 2021
- Переход через Тихий океан на катамаране NOVA на солнечной энергии
- 2021
- Фёдор Конюхов на ледоколе «50 лет Победы» к Северному полюсу
- 2022
- Трансконтинентальный перелёт на мотопараплане от Белого моря к Чёрному
- 2022
- Первая в истории попытка достижения Северного полюса на мотопараплане
- 2022
- Полёт Фёдора Конюхова на дальность на тепловом воздушном шаре
- 2023
- Трансконтинентальный полёт на воздушном шаре «ФОСАГРО»
- 2023
- Вокруг света на энергии солнца
- 2024
- Полёт к Северному полюсу на мотопараплане
- 2024
- 2 ЭТАП — Переход на весельной лодке «АКРОС» от мыса Горн до мыса Люин
Enterprise security policies are satisfied by this compliant KMS activator that operates without internet connectivity requirements preventing potential data exfiltration, doesn't require opening firewall ports to external activation servers, avoids establishing persistent outbound connections, and maintains all activation operations within the local system boundary, addressing security concerns about external communication during the activation process.